Why Should You Consider Application Security Automation?
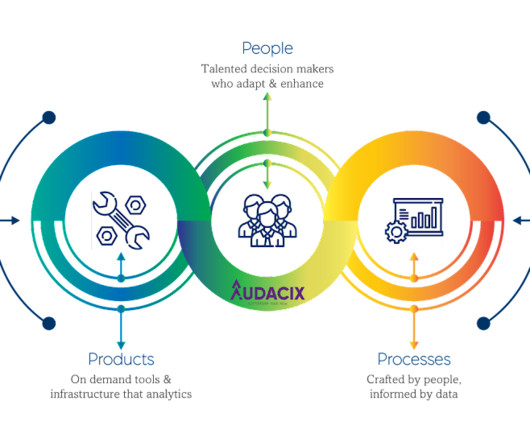
Audacix
JANUARY 31, 2024
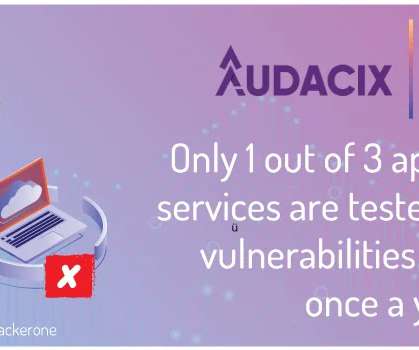
Automating application security using an automated penetration testing tool empowers you and your organizations to tackle cyber threats, speed up your application development cycles, adhere to regulatory compliance, and optimize resource allocation. Too many delays in assessing and patching application vulnerabilities?














Let's personalize your content